Rootkit Ntoskrnl Exercise
Uroburos was already described as a very sophisticated and highly complex malware in our G DATA Red Paper, where we had a look at the malware’s behavior. This malware belongs to a specific type called rootkit. The general purpose of a rootkit is to modify the behavior of the system and, especially, to hide its activity. Generally, a rootkit resides in the kernel. To analyze this kind of malicious software, analysts need to use specific tools, such as WinDbg, to debug the Microsoft Windows kernel.
WinDbg is a debugger provided by Microsoft. One can use this tool to debug user mode applications and kernel mode applications (for example the drivers). Today, we would like to give you an understanding of how analysts work their way through malware and give you some insights into the code of one of the most sophisticated digital threats. In this current example case, we decided to work with a memory dump (crash dump) of a system infected with Uroburos. To facilitate the analysis, we added an extension to add the support of python, called: PyKd. WinDbg has its own script language, but it is not easy to understand. One can download this python extension here, for free: To realize this article, the machine was infected by the Uroburos dropper with the following md5: 626576e5f0f85d77c460a322a92bb267.
We apologize for the difficulties. We see that Inline hook ntoskrnl.exe is a harmful trojan threat which is designed by the web criminals to gain access over to the affected computer and ruins its settings harshly. We request you to get connected with our remote technician to have additional support. They will check and help you with this issue. NTOSKRNL-HOOK is a detection for technique used by Rootkit Trojan and be able to hide malicious files and process from Windows and security programs. NTOSKRNL-HOOK Rootkit are programs that can be utilized by malware authors to conceal malicious files from being seen during a real-time scanning of security programs. What is ntoskrnl.exe? Ntoskrnl.exe (Windows boot up kernel) is a vital component utilized in the boot process for NT based Microsoft operating systems. It is also responsible for a host of system services such as process and memory management, security management, object management, hardware virtualization and so on.
Rootkit Ntoskrnl Exercise Equipment
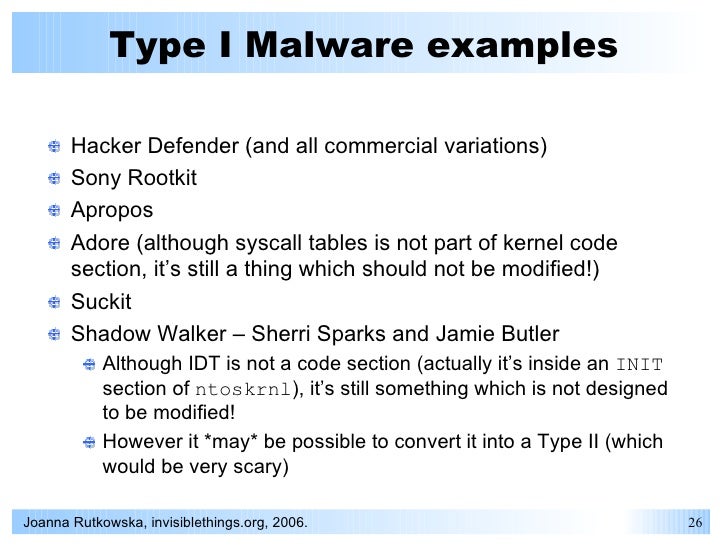

Visualization of the hooks The Uroburos rootkit adds several hooks to hide its activity. In our specific case, the hooking is a technique used to alter the behavior of specific system functions; the rootkit fakes the output of the Microsoft Windows API. For example, it hides registry entries, files and more.
To perform this task, the rootkit developers decided to use interrupts. We can display the Interrupt Descriptor Table (IDT), as shown below. The IDT table stores pointers to ISR (Interrupt Service Routines), which are called when an interrupt is triggered. This output shows us two remarkable things:. First, the driver uses a well-known Windows kernel memory pool tag called 'NtFs'.
The Windows components mark allocated memory block with a unique tag. But the rootkit uses the same tag as the legitimate ntfs.sys driver.
This choice was made to hide the rootkit and dupe the analyst. Secondly, the output looks like the beginning of a PE. But this PE is broken: the MZ is not available and some information is missing. For example, the value of the SizeOfImage (85980000+0x140) is null. The rootkit alters the beginning of the PE to hide itself.
Some tools parse the memory and look for the MZ string to identify the beginning of a PE. In our current case, if we used these tools looking for a PE file, we would never identify our malware using this automation. Manual analysis is needed here. To dump our driver we need to reconstruct the PE but we don't know the size of the binary, as mentioned above, so we need to make a large dump, to be sure to not forget a part of the binary.
Modules, drivers and devices We can now display the loaded (and unloaded) modules with WinDbg. Two objects are particularly interesting: FWPMCALLOUT and RawDisk1 WFP callout This first device is FWPMCALLOUT. Thanks to the name of the device we can guess that the rootkit registers a callout for Windows Filtering Platform (WFP). The WFP is a set of API and system services which provides a platform for creating network filtering applications.
In our case, the rootkit uses this technology to perform Deep Packet Inspection (DPI) and modifications of the network flow. The purpose of this device is to intercept relevant data as soon as a connection to the Command & Control server or other local infected machines used as relay is established and to receive commands. As there is no command to simply list the WFP callouts, we have to extract the information needed using different steps: First, the netio!gWfpGlobal variable contains the starting point for the WFP data structures. Thanks to this command we are able to list the files hidden from the operating system. Digital signature enforcement Microsoft created a Driver Signing Policy for its 64-bit versions of Windows Vista and later versions.
To load a driver, the.sys file must be signed by a legitimate publisher. Developers may disable the Driver Signature Enforcement process during the development phase of a driver, which means a developer does not have to sign each compiled driver version during development phase. This mode is called “Test-mode”. In our case, the rootkit is not signed, which would usually mean that it had no chance to be accepted by Microsoft’s policy, but it disables the digital signature process to circumvent the checks. The status of this feature is stored in the global variable nt!gcienabled. Compare the value of this variable on a clean system, without infection with the same information on an infected system. We can clearly identify that the malware disabled the driver signature enforcement.
• There may also be two additional spring-loaded metal pieces that hold the ribbon in place. They'll be located close to the ribbon spools. Typewriter ribbon smith corona corsair manual.
Generally speaking, we could do the same by using bcdedit.exe -set TESTSIGNING OFF, to switch into testing mode to be able to load unsigned driver. The difference is: Using bcdedit.exe triggers a message window which is shown to the user, at the bottom of the desktop, and this is not very secretive. The action could be detected immediately. More information about the malware’s circumvention of the driver signature enforcement can be found in our SecurityBlog article: Conclusion What you have seen now, is a very limited part of the extensive analysis of complicated malware and a very short introduction into WinDbg. Generally, it is very hard to apprehend such an extensive tool, but when working on such a case of kernel land analysis, researchers do not have a choice.
Processed like this, in an article with code snippets, the results seem logic and do make perfect sense. But, believe us, working with malware code costs a lot of extensive training, experience and time. Related articles 2014////02/28.